Hackers are always looking for new ways to take over your computer and then steal your data or turn your machine into a zombie. They mainly target Windows computers due to their popularity. Additionally, Windows is affected by many zero-day vulnerabilities that hackers hope to exploit.
But what about Chromebooks? Can your Chromebook become a target for hackers? How frequent are hacking attacks on ChromeOS? We’ll answer these questions, and many more, in the guide below.
Is Chromebooks Safe from Hackers?
Chromebooks are very hard to hack. ChromeOS laptops feature multiple built-in layers of protection that include sandboxes, verified boot sequences, bulletproof encryption, and more. Simply put, if hackers manage to bypass one layer of protection, others are still in effect, and they’ll eventually detect and block the attack.
That’s one of the reasons you haven’t heard much about successful hacking attacks on Chromebooks in the media. Your Chromebook is a true fortress that can successfully fend off hackers’ attacks. Let’s dive a bit deeper and explore what makes Chromebooks so secure.
ChromeOS Security Overview
As Google explains, Chromebooks use the principle of “defense in depth.” ChromeOS uses a series of protection layers, one on top of the other, to keep hackers at bay.
Sandboxes Everywhere
When you visit a web page or run an app, your Chromebook opens the respective page or app in a sandbox, which is a restricted environment. Even if you’re visiting a malware-ridden page, it won’t affect the other tabs or anything else on your laptop, for that matter.
Verified Boot
Sneaky malware can sometimes escape the sandbox. But even in this scenario, your Chromebook remains protected. Your laptop automatically runs a Verified Boot sequence on startup. Should it detect any unwanted changes, it will repair itself automatically, flushing out the intruders.
Your Chromebook has twin OS partitions that the system uses to compare different versions of the OS. If it suspects one of the OS versions has been tampered with, it will use the untampered version to boot up.
Encrypted Data Stored in the Cloud
Your Chromebook stores important data in the cloud. So, even if hackers manage to gain access to your computer, they won’t be able to harvest too much data. However, your browser cache, cookies, and downloads may still be available on the machine. But even if your Chromebook gets hacked, data access is limited simply because your data is somewhere else.
Flawless Coding

ChromeOS is open-source. Thousands of people regularly examine the code to identify flaws and patch vulnerabilities before hackers find them. Google will pay you a $150K bounty if you manage to hack a Chromebook. Yes, you read that right; that’s $150K. The good news is that the bounty has only been collected once. This confirms the company takes ChromeOS security very seriously.
Not to mention that your Chromebook manages updates automatically to ensure you’re always running the latest and most secure ChromeOS version.
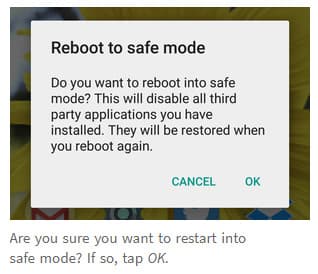
Use Recovery Mode to Save the Day
If something unexpected happens and your system gets compromised, you can use Recovery Mode to quickly restore the OS to a known good version.
Chromebooks Are Not a Lucrative Target

The majority of viruses target Windows PCs mainly due to the popularity that the OS enjoys. Windows-based attack schemes won’t work against Chromebooks.
Since Chromebooks are mostly used by students and people that don’t need sheer processing power, hackers can’t derive much value from the data they could potentially get their hands on. As you can see, Chromebooks are pretty niche.
On the other hand, an attack on a financial institution that relies on Windows for day-to-day activities can potentially bring hackers millions of dollars.
Best Practices to Keep Hackers at Bay
- Stay away from suspicious sites. If you visit a website that’s been hacked, hackers can easily record sensitive or confidential information.
- Don’t type in personal information on a web page that uses HTTP instead of HTTPS.
- Don’t download apps from third-party download websites; install them only from trusted vendors. Refrain from installing unnecessary apps and extensions.
- Equally important, don’t bypass Google’s security restrictions. Don’t run extensions and apps unsandboxed. Your Chromebook is vulnerable to malicious extensions, apps, or phishing webpages, just like any other computer out there.
Conclusion
Your Chromebook uses multiple built-in layers of protection that can successfully fight off malware attacks. ChromeOS is open-source, and thousands of people regularly scrutinize the code to detect any potential security flaws. The OS has only been hacked once since Chromebooks were first launched back in 2010. The “hacker” was actually a security researcher. That’s pretty impressive, isn’t it?
What do you think about the security architecture that Google uses on Chromebooks? Share your thoughts in the comments below.


mine started having hacker pictures pop up and text was deleted in a doc i was working on with my freind
Tell me again how secure a Chromebook can be.
Yesterday, while checking out something in LastPass, I came up on dark-shade.firebaseapp.com/pswd P0n33. I checked to see what it could be, because I didn’t remember it and because I never use such short passwords. Up popped, “Try resetting your password.” I decided to delete the thing… “Your request to reset your password has expired, or the link has already been used.”. So I deleted it, and got the same message. Did it again, and got, “You’ll have to try harder than that.”. And, Bloop!!, it all vanished. Unfortunately that’s about the time my Chromebook passed out, and I can’t get it to awaken. It may not have anything to do with dark-shade, and I’m fairly certain that Google and LastPass, if either pays any attention to this, will point fingers at one another.
Since ‘firebase’ is a Google thing, I’d lay money on them, but I’m a 70 year old grandmother, and not technically savvy. All the same, I’ll give this advice: Install good anti-virus software, and don’t let the grandkids play on your device.
what if both operating systems are tampered with
Mine already hacked 20 days in.
I get pop up ads right away on 1st week. I start download something to remove. I think extension.
Doesn’t make sense to say can’t be hacked when computer is allowing alot of pop ups.
Both are sure possibilities.
If your Chromebook is stolen can it be hacked or turned on and used by the person that stole your laptop?
Very well done. Succinct but the security characteristics of Chrome OS are very well described, Thanks