Most people who use the internet already know that the padlock icon in the URL bar means that the site is secure, but you may not realise exactly what that means or how secure your connection really is with that padlock.
The padlock is a visual indication that your connection to the website has been secured using HTTPS. HTTPS, or Hypertext Transfer Protocol Secure, is a version of the HTTP protocol that uses encryption to secure your data from prying eyes.
Encryption is a process of scrambling data with an encryption cipher and key so that it can only be read by using the decryption key. You can think of it as a lockbox, you can write a message, lock the box, and then only someone with the right key can open the box to read the message. This keeps your data secure from hackers trying to steal account details.
One key piece of information you should know is that the encryption and security of HTTPS only verifies that your connection to the website you typed in the URL bar is secure. It doesn’t imply that the website is secure, or even that it’s the website you meant to browse to. Many phishing and malware websites are moving to use HTTPS as it becomes more accessible, so it’s not safe to just trust any site that uses HTTPS.
Tip: A “phishing” website tries to trick you into submitting sensitive data, such as account information, by faking a legitimate login page. Links to phishing sites are often sent via email. Malware is a catch-all term for “Malicious software” it includes viruses, worms, ransomware, and more.
Note: You should never enter your username and password, or other sensitive information such as bank details over an insecure connection. Even if a site has the padlock and HTTPS, it doesn’t mean you shouldn’t still be careful with where you enter your details.
Chrome Developer Tools
To view more information about your secured connection, you need to open the Chrome developer toolbar. You can do so by pressing F12, or by right-clicking and selecting “Inspect” at the bottom of the list.

The developer toolbar will default to the “Elements” panel, to see the security information you need to switch to the “Security” panel. If it is not immediately visible you may need to click the double arrow icon in the developer tools panel bar and then select “Security” from there.

If you don’t like the developer toolbar being attached to the right of the page, you can move it to the bottom, left, or move it into a separate window by clicking the triple-dot icon in the top-right of the developer toolbar, and then selecting your preferred option from the “Dock side” selection.
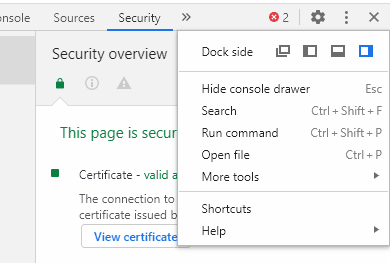
In the security panel overview, there are three sections of information, Certificate, Connection, and Resources. These cover the details of the HTTPS certificate, the encryption used to secure the connection, and detail if any resources were served insecurely respectively.
Certificates
The certificate section states which certificate authority issued the HTTPS certificate, if it is valid and trusted, and allows you to view the certificate. Beyond verifying that the website you’re connecting to is run by the person who owns the URL, the certificate doesn’t directly affect the security of your connection
Tip: HTTPS certificates work on a chain-of-trust system. A number of root certificate authorities are trusted to issue certificates to website owners, after they prove that they own the website. This system is designed to prevent hackers from being able to generate certificates for websites they don’t own, as these certificates won’t have the chain of trust back to a root certificate authority.
Connection
The “Connection” section details the encryption protocol, key exchange algorithm, and encryption algorithm used to encrypt your data. The encryption algorithm should ideally say “TLS 1.2” or “TLS 1.3”. TLS, or Transport Level Security, is the standard for negotiating encryption configurations.
TLS versions 1.3 and 1.2 are the current standards and are considered secure. TLS 1.0 and 1.1 are both in the process of being deprecated as they are old and have some known weaknesses, although they are still adequate security-wise.
Tip: Deprecated means that their use is being discouraged and steps are being taken to remove support.
The predecessors to TLS were SSLv3 and SSLv2. Almost nowhere supports either of these options anymore, because they have been deprecated due to being considered insecure since 2015 and 2011 respectively.
The next value is the key exchange algorithm. This is used to securely negotiate the encryption key to be used with the encryption algorithm. There are far too many to name, but they generally rely on a key agreement protocol called “Elliptic-curve Diffe-Hellman Ephemeral” or ECDHE. It is not possible to determine the agreed encryption key without using third-party network monitoring software and a deliberately weakened configuration. Explicitly not supporting access to this information in the browser means that it can’t be compromised by accident.
The final value in the Connection section is the cipher suite used to encrypt the connection. Once again there are far too many to name. Ciphers generally have multipart names that can describe the encryption algorithm used, the strength of the cipher in bits, and what mode is being used.
In the example of AES-128-GCM as seen in the screenshot above, the encryption algorithm is AES, or the Advanced Encryption Standard, the strength is 128-bits, and the Galois-Counter-Mode is being used.
Tip: 128 or 256 bits are the most common levels of cryptographic security. They mean that there 128 or 256 bits of randomness making up the encryption key being used. That’s 2^128 possible combinations, or two multiplied by itself 128 times. As with all exponentials, the numbers get very big, very fast. The number of possible 256-bit key combinations is roughly equal to some low-end estimates of the number of atoms in the observable universe. It is unimaginably difficult to correctly guess an encryption key, even with multiple supercomputers and centuries of time.
Resources
The resources section shows any page resources, such as images, scripts, and stylesheets, that were not loaded over a secure connection. If any resources were loaded insecurely this section will highlight red and provide a link to show the specific item or items in the network panel.

Ideally, all resources should be loaded securely as any insecure resource could be modified by a hacker without your knowledge.
More information
You can see more information on each domain and subdomain that were loaded by using the column on the left of the panel. These pages show roughly the same information as the overview although Certificate transparency information and some extra details from the certificates are shown.
Tip: Certificate Transparency is a protocol used to counter some historical abuses of the certificate issuing process. It is now a mandatory part of all newly issued certificates and is used to further verify that the certificate is legitimate.
The origin view allows you to look through each of the domains and subdomains that loaded content in the page, so you can review their specific security configurations.


Very much!! Someone needs to share this information with IRS, regarding their requirements for accessing the EFTPS system. They are asking for browsers to use TLS 1.1 or 1.2 and I have 1.3 already!!