There are two types of security certificates that can be installed on your computer: root and client. A client certificate is perfectly safe to use and install, they are simply used to prove your identity to another device. A root certificate carries a lot more power, however, and you should always be careful if you are asked to install one.
A root certificate is a certificate that your device trusts to sign other certificates, these secondary certificates can have many different uses including trusting a website or trusting software. This chain of trust is where the security risk comes from.
What is a certificate used for?
Security on the internet is built on a web of trust. There are many root certificates installed on your computer, combined these create a large certificate infrastructure allowing for a somewhat competitive market. When you connect to a website over HTTPS, your connection is encrypted through an encryption cipher, however, the webserver also sends your computer an HTTPS certificate. Your computer looks at the certificate and determines if it can be trusted by checking if it was issued by a root certificate that your computer trusts.
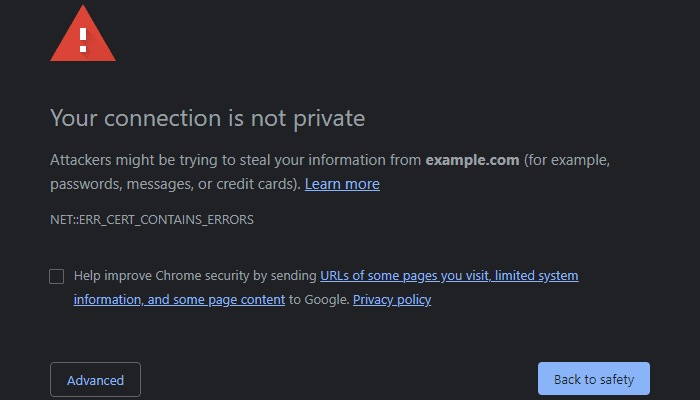
If the HTTPS is trusted, then your computer successfully connects to the webserver. If the certificate is not trusted, however, your computer will display an “untrusted certificate” warning. This is designed to prevent you from being tricked into connecting to sites that you didn’t mean to. For instance, only the owner of Technipages can get a certificate signed by a trusted root certificate for the Technipages website. While it’s possible to make your own certificate for the Technipages website, no-one would trust it and so everyone would see a warning message.
Certificates that are used to sign software are used to verify that the software legitimately comes from a trusted company, such as Microsoft. This should give you the confidence to allow the software access it needs. Conversely, the lack of this trusted signing should be a warning sign that software may not be legitimate or trustworthy.
Risks of adding a certificate
A chain of trust from only one of any of the trusted root certificates is required for an HTTPS certificate, software signature, or any other form for root certificate validation to work. This is why adding a root certificate is risky and should not be done lightly. If you trust the wrong person and the root certificate is misused it can be used to trick you into trusting websites, software, and more that you shouldn’t and normally wouldn’t. This could make it significantly easier for hackers to hack your computer.
You should almost never need to install a root certificate for any purpose. If you are asked to install one, you should take the time to understand why it’s needed and what it will be used for. If you’re unsure, it may be a good idea to ask for a second opinion from someone that you trust that’s good with computers. Another place you could go to ask is the security forum on stack exchange.